Usually, I use my DrayTek Vigor 165 as a bridge modem for a pfSense firewall/router behind it. Now I had the need to use it as a full firewall/router, thereby I had to configure its firewall as well. Coming from a pfSense background, the Vigor 165 firewall works in a somewhat different way.
In the Firewall -> General Setup page you will find the Call Filter and Data Filter settings. You may ignore the Call Filter settings. They are used when the internet connection is established on-demand, following a device request to send outbound traffic. The Call Filter allows avoiding establishing a connection if the outbound traffic is forbidden.
What matters for most users is the Data Filter. These are the rules applied to inbound/outbound traffic when an internet connection is established already.
Each Filter is mapped to a Filter Set. A Filter Set is a set of filtering rules. Filter Sets can be chained, and a rule within a filter set can jump to another Filter Set. Once processing is switched to another filter set, it won’t return back. Be careful to avoid loops.
There is also a Default Rule used when there is no match. The order of processing is as follows:
- Data Filter Sets and Rules
- Block routing connections initiated from WAN settings
- Default Rule
The Default Rule setting is by default set to Pass. It will pass any packet that doesn’t match a rule. As the router comes with no pre-configured rules but a simple (and incorrect) one for NetBIOS traffic, that is what allows any other traffic when the firewall is enabled. Of course the default should be blocking any unknown traffic initiated from the WAN side, while letting the outgoing traffic flow. Because of the default settings, the LAN behind the Vigor is basically “protected” by NAT beahviour only, even when the firewall is activated.
Thereby I will show how to setup the firewall to block properly all connection initiated from the WAN side not allowed by a specific rule, and allow any connection initiated from the LAN side not blocked by a specific rule..
One issue is the Data Filter allows only one associated Filter Set. There is no concept of inbound/outbound separate settings. We could write all inbound/outbound rules in this single Filter Set, or we can take advantage of a Filter Set being able to invoke another Filter Set to keep them separated.
My main Filter Set – the one invoked by the Data Filter – has three rules only. These will just filter on the packet direction. These rules then invoke another Filter Set with specific settings for each kind of traffic.
One rule is for the LAN → WAN traffic, one for the WAN → LAN traffic, and the last one for the LAN → LAN traffic (the latter may not be useful to you if you don’t have local traffic going through the Vigor 165 firewall – devices connected to the router LAN ports will go through the firewall as well).
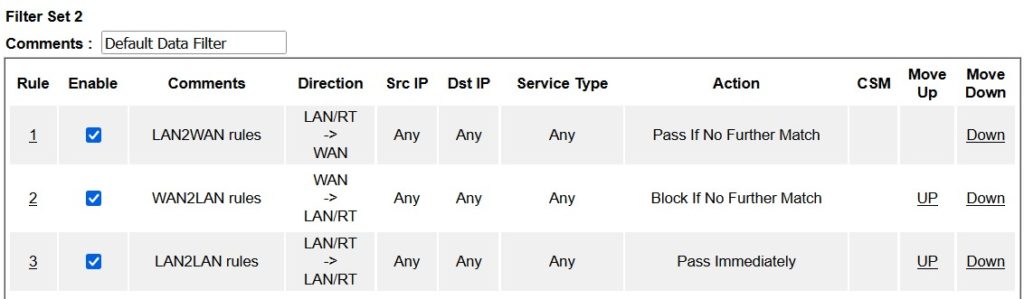
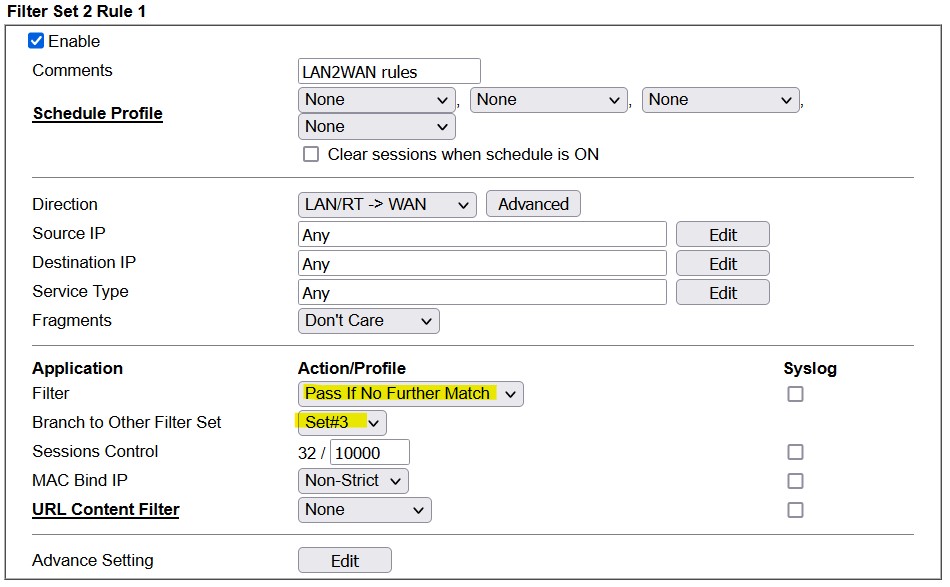
The LAN2WAN filter matches outbound traffic – LAN/RT → WAN direction – and allows any traffic that is not blocked by a more specific rule (Pass If No Further Match). This lets the Default Rule to be set to “Block” without blocking outbound traffic. Then the filter simply jumps to another Filter Set which performs the final specific filtering (look at the highlighted settings in yellow):
Filter Set #3 contains the actual outbound traffic rules:
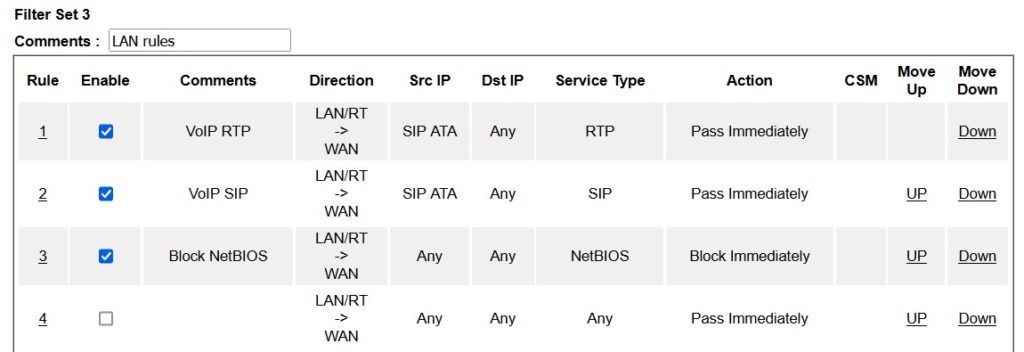
In this case there are two rules to allow VoIP traffic immediately, to avoid waiting for processing other rules, and a rule to block outbound NetBIOS traffic (note: the default “block NetBIOS traffic” rule is wrong). Anyway, remember any traffic not explicitly blocked here is allowed by the parent Filter Set rule Pass If No Further Match.
The WAN2LAN main rule is very much alike, but of course it does block any traffic initiated from the WAN not allowed by a child rule:
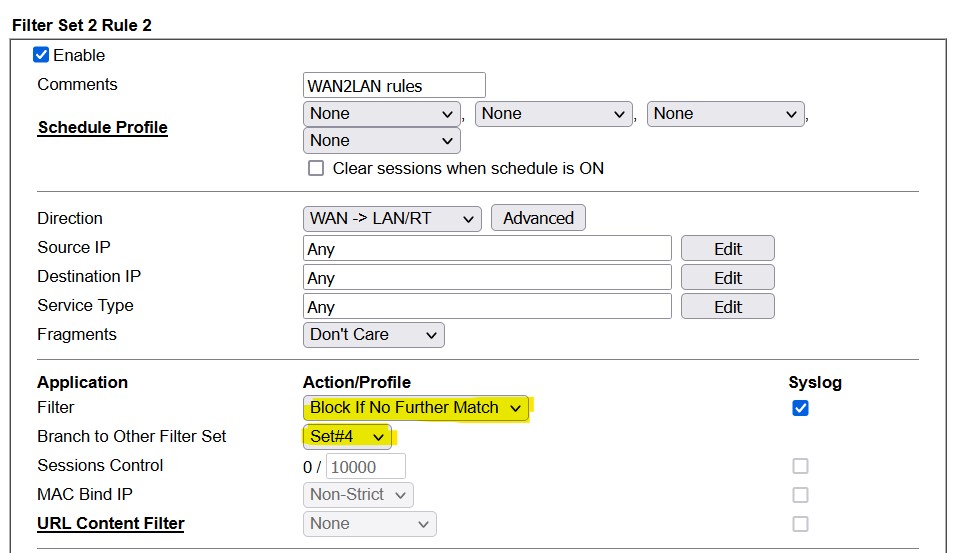
The Vigor firewall is a stateful one, it keeps tracks of connections initiated from the LAN side, and their incoming traffic is automatically allowed.
The Syslog setting allows recording any packet that is blocked by a rule, for troubleshooting and/or monitoring needs. A Syslog server needs to be configured in System Maintenance → Syslog/Mail Alert.
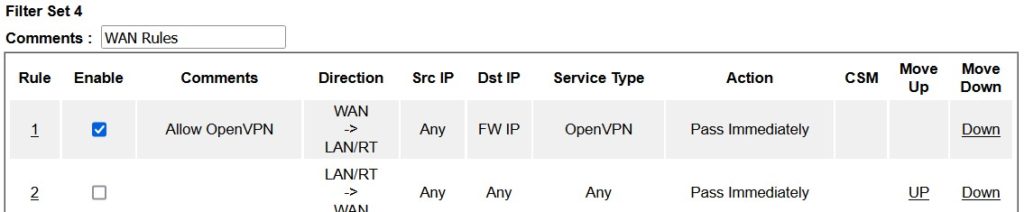
The Filter Set invoked contains the permitted inbound traffic, in this case an OpenVPN server on a specific IP:
I use the Vigor Object Settings for IP and Services (ports) extensively in the rules configurations. While you can easily set IP/ranges/subnets and ports directly in the firewall rules, Objects and Groups allow creating simpler rules, by reusing settings, and grouping them. It is also required for IPv6, because this kind of addresses can’t be input in the rule settings UI directly.
For example, instead of having to declare each NetBIOS/SMB protocol (TCP/UDP) and ports separately in each rule, I could create a NetBIOS Service Type Group object and use it in a single rule:
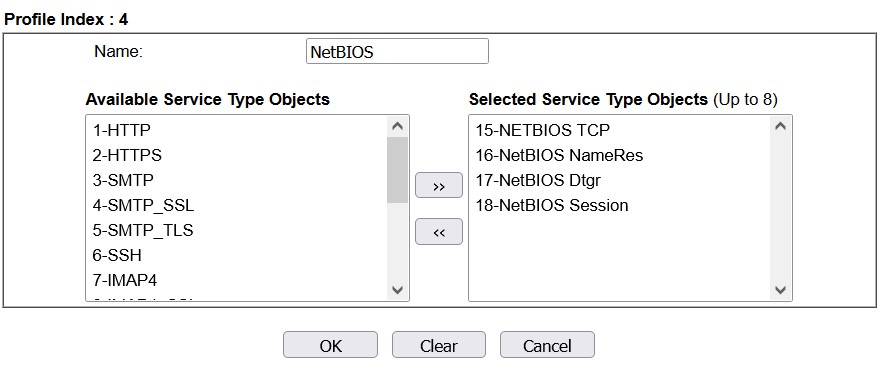
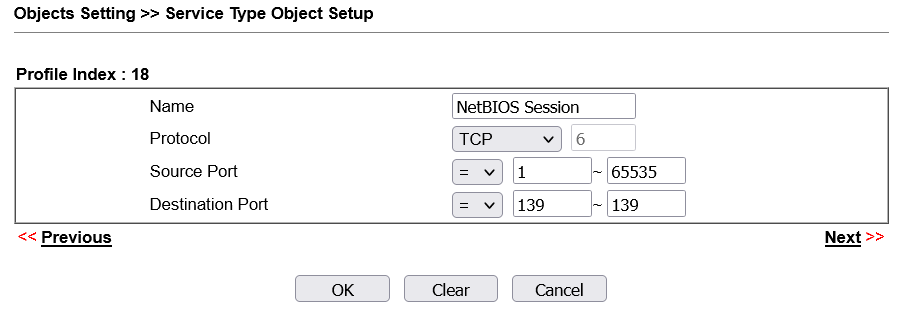
The four selected Service Type objects define all the NetBIOS ports and protocols – UDP 137 and 138, TCP 139 and 445 (the default filter is wrong because these are the destination ports, while 53 is the DNS port). Each Service Type Object was defined in the Service Type Object Setup:
The Vigor 165 firewall allows filtering access using Content Filters also, for example they can match an HTTP URL. Content Filters are matched after an IP Filter passes, see https://www.draytek.com/support/knowledge-base/5333 for a full explanation of the Content Filters workflow, note that the Vigor 165 only supports URL Content filter. This might be the topic of a separate article, I do not have much use for them right now.
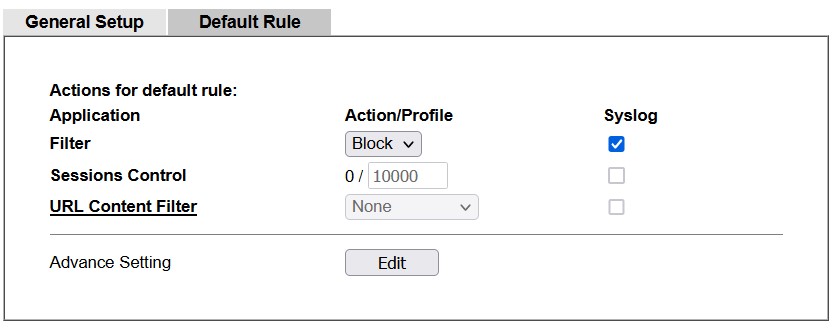
There are settings not well explained in the documentation. For example the Session Control setting. The manual says “The number typed here is the total sessions of the packets that do not match the filter rule configured in this page. The default setting is 60000.” But that doesn’t makes sense to me. Looking at the CLI commands, the editable values is named Max Session Limit, and the non-editable number Current Sessions. My take is this is a session limiter – the filter rule will allow up to Max Session Limit concurrent sessions, and the actual number of active sessions matching the rule is shown. The default value for the maximum session limit in the Vigor 165 is 10000, which matches the 10K NAT sessions supported by the device. Leave it at the default value if you have no reason to change it, i.e. limiting concurrent access to a shared resource.
The Session Timeout setting under Advanced could be the lifetime of the session state.
The CLI has the ipf view command that can be used to look at the firewall statistics.
In Firewall → General Setup, activate the Enable Strict Security Firewall – this looks to be the main firewall switch, but the wording makes it a bit confusing -one may wonder what happens if the firewall is not Strict Security. The Data Filter needs to be Enabled as well. The Call Filter can be disabled, unless an on-demand xDSL connection is used.
Block routing connections initiated from WAN is used only for non NAT connections, so it is used only if you configure the IPv4 2nd address in LAN → General Setup “For IP Routing Usage”, or if you enable IPv6 on the WAN interface. IPv6 doesn’t use NAT, so that setting would block any incoming IPv6 connection not allowed by a rule, when enabled. But our default WAN → LAN rules already does that.
With the rules above in place, the Default Rule could be set to “Block” too:
outbound traffic will still flow freely (but specific rules), while not allowed inbound traffic should be blocked. Actually we could have not used the WAN → LAN root rule at all, relying on the default block rule only for anything not matched by other filters, while adding any needed rule for inbound traffic, but I believe the setup above is clearer about what the workflow is. The default rule may never be invoked, but it is still there as a safe fallback.
Of course NAT would work almost the same way by itself for inbound traffic, just remember it is a side-effect only. Setting the firewall adds another layer of proper security, allows to control outbound traffic as well, and becomes necessary when IPv6 is used.
Format of a Syslog entry
When recording to syslog is enabled, the entries are written in this format:
[FILTER][Block][WAN->LAN/RT, 44:06:54 ][@S:R=2:2, 52.97.201.194:443->192.168.10.17:34164][TCP][HLen=20, TLen=83, Flag=AP, Seq=2127413670, Ack=4109947162, Win=16385]
The data show if the entry is a Block/Pass entry, the direction of the packet, and the system up time when the packet was logged. @S:R= indicates which Filter (S)et and (R)ule was matched, in this case Filter Set 2 and Rule 2. Followed by packet data: source and destination, protocol, header length and total packet length, and some data that depends on the protocol type – i.e. TCP will have TCP flags, sequence, acknowledgment and window size.
UDP example:
[FILTER][Block][WAN->LAN/RT, 44:27:00 ][@S:R=2:2, 138.246.253.15:56303->192.168.201.2:443][UDP][HLen=20, TLen=1228]
ICMP example:
[FILTER][Block][LAN/RT->LAN/RT, 23:08:22 ][@S:R=13:1, 192.168.201.11->192.168.200.247][ICMP][HLen=20, TLen=84, Type=0, Code=0]
In this example note that Filter Set “13” means the Default Rule.